Best Practices To Prevent Data Breach

Data breaches don’t spare any type of organization, large or small. Big names have been affected the past decade – with the Yahoo breach (3 billion exposed accounts) in 2013 – 2014, the LinkedIn breach (117 million exposed accounts) in 2012; the Equifax breach (147.9 million exposed records) in 2017, the Marriott International breach (505 million exposed records) in 2014 – 2018 and 2020, and the eBay breach (145 million exposed accounts) in 2014 being some well – known instances.

With the threat of data breaches looming over every single industry, organizations must stay ahead of malicious attackers. Not doing so can result in huge losses of both money and reputation. To prevent data breaches, it is necessary to first understand what they are, and how much damage they can cause.
Contents
- 1 What is a Data Breach?
- 2
- 2.1 Best Practices To Prevent Data Breach
- 2.1.1 Data Protection Regulations Compliance
- 2.1.2 Maintenance of System Logs
- 2.1.3 Data Backups
- 2.1.4 Password Policy
- 2.1.5 Comprehensive Security Policy
- 2.1.6 Periodic Awareness and Auditing Exercises
- 2.1.7 Usage of Secure Technologies
- 2.1.8 Effective Patch Management
- 2.1.9 Timely Vulnerability Assessments
- 2.1.10 Incident Response Plan
- 2.1 Best Practices To Prevent Data Breach
What is a Data Breach?
In simple words, data breaches are the unintentional exposure of data to persons without the authority to access it. These persons could be internal or external, and the breach may or may not be the result of a targeted attack from their side.
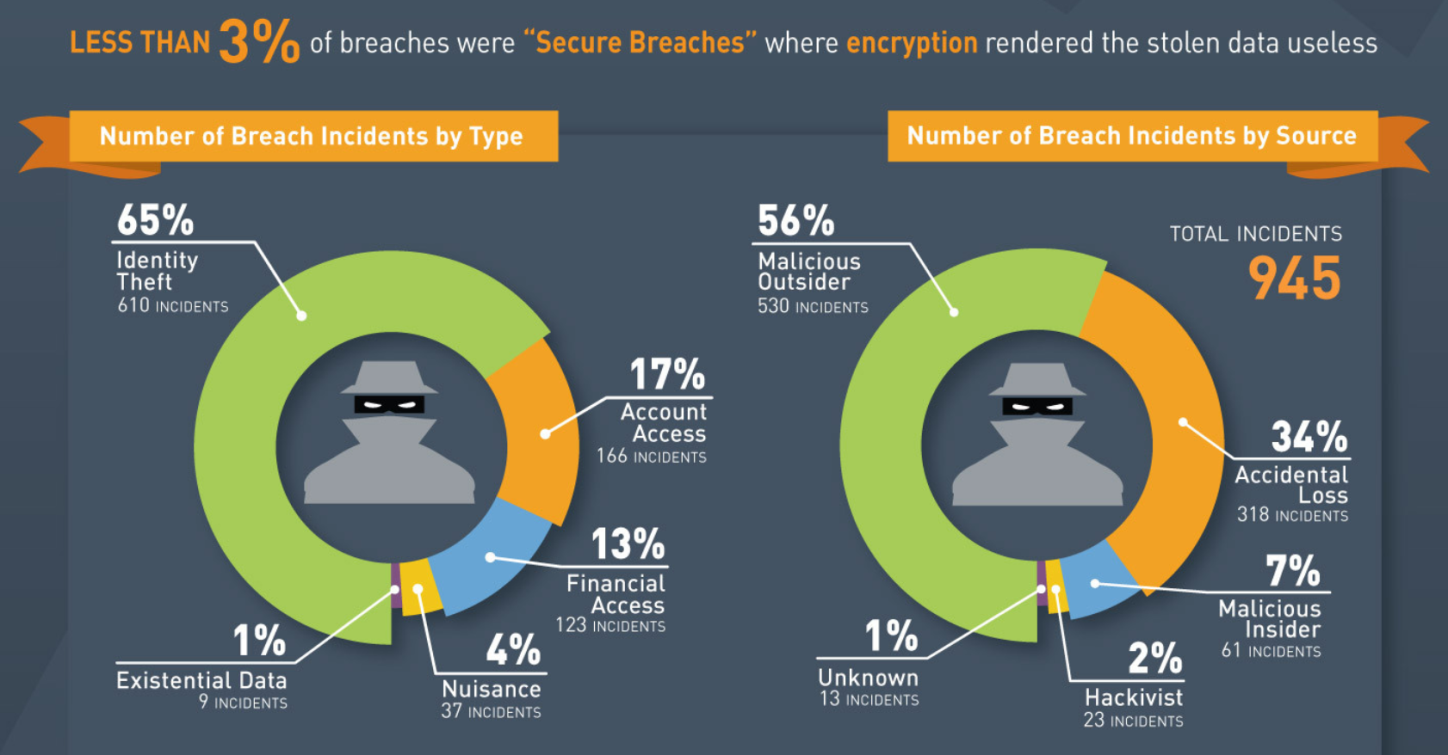
These parties responsible for these breaches could be malicious outsiders (56%), accidents (34%), malicious insiders (7%), hacktivist organizations (2%), and other unknown entities. The perpetrators could have any number of reasons for carrying out the breach – from identity theft (65%), account access (17%), and financial access (13%), creating nuisance (4%), to accessing data (1%).
Process of a Data Breach
Accidental and/ or non – technical data leaks can take place due to a variety of reasons. This includes, but is not limited to improper privilege allocation, flawed security configurations, poor data storage, etc. Targeted attacks from malicious actors, however, are much more complex. In order to successfully breach a network, find usable data, and then extract it, hackers must form a detailed plan of action.
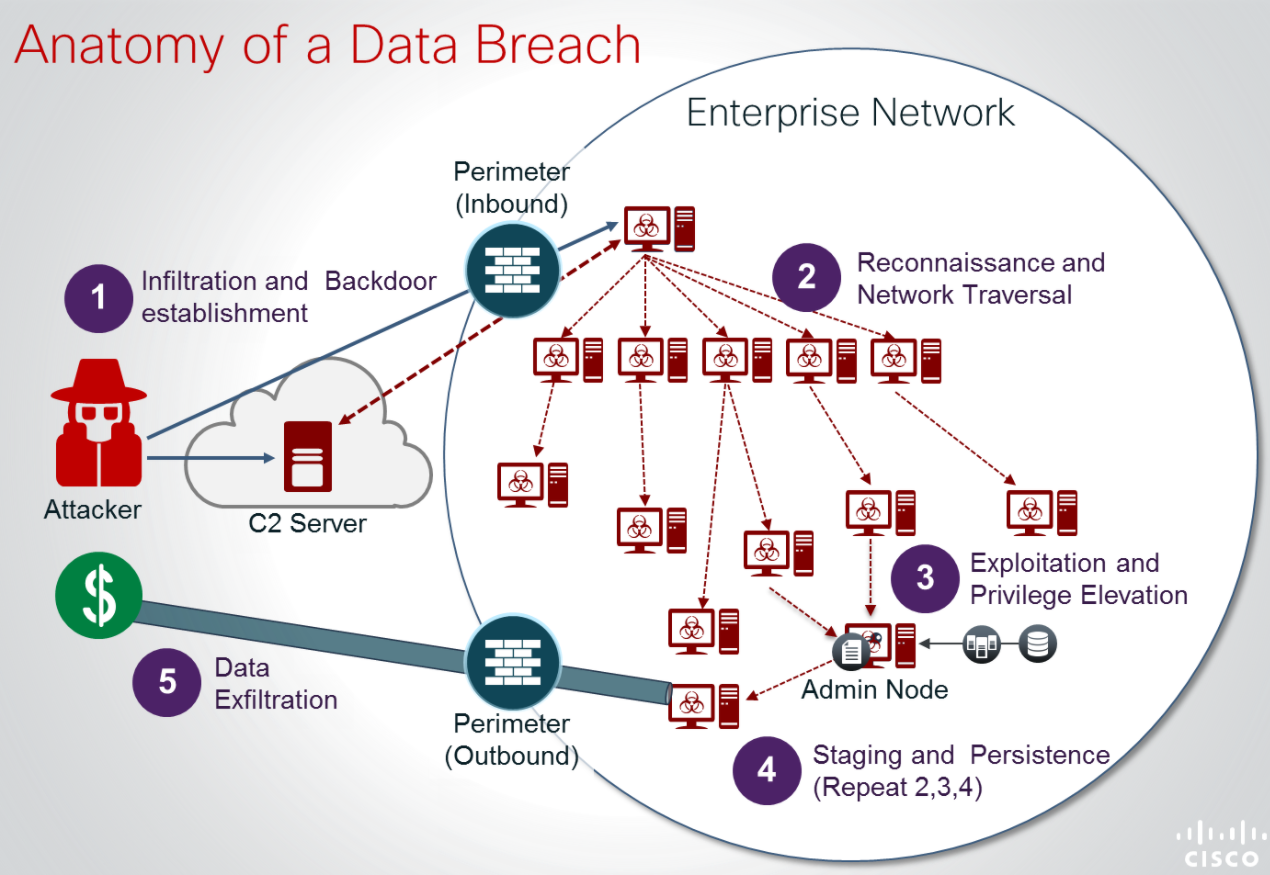
(Source: Cisco: Securing Your Network Before BYOD or IoT)
- Infiltration: Firstly, the attacker (s) must find entry points into the network they wish to breach. These entry points could be anything – mobile phones, smart Internet of Things connected devices, web applications being used by internal members, emails being accessed by members, open and unprotected ports in the network, etc. After successfully locating an available entry point, attackers must work on breaking or sidestepping the defenses. This includes network perimeter security layers such as Intrusion Detection Systems, Intrusion Prevention Systems, firewalls, antiviruses, and the like. Once this step has been carried out, the attacker is “inside” the network.
- Reconnaissance: Once the attacker has entered the system, they must get familiar with it. This traversal allows them to map out the entire network (including the defenses and vulnerabilities) and gain important knowledge about its architecture. Having an idea about the various types of software and applications in use enables the attacker to customize their attack plan. For example, certain components of a network could have previously discovered (unpatched) vulnerabilities that could be exploited.
- Privilege Escalation: Entering a system doesn’t necessarily provide the attacker with the appropriate permissions to do significant damage to the target. Often, attackers may use social engineering attacks to gain access to accounts of lower-level employees, who have limited permissions within the organization’s network. To exploit the system as intended, attackers often require high – level user permissions (even administrator – level, at times). This was seen in the Twitter hack of 2020, in which hackers used social engineering to enter Twitter’s network through the accounts of low – level employees, and went on to escalate their privileges to perform account takeovers of important public figures such as Elon Musk, Barack Obama, and Bill Gates.
- Staging: This step involves the repetition of reconnaissance and privilege escalation at every security level. This is necessary because different layers have different forms of defense layers, of varying strength. Additionally, it could be possible that some layers have multiple vulnerabilities that can be exploited but won’t be of much use. On the other hand, overall secure layers might have a single, complex vulnerability that can enable the attacker to launch extremely damaging attacks, if they succeed in exploiting it. Repeating each step at each stage reduces the chances of missing a flaw, increasing the chances of a successful breach.
- Data Extraction: When the attacker has carried out the above – mentioned steps to their satisfaction, they can finally attack the organization’s network as desired, and access the data they were targeting. Once they lay their hands on the required data, they can extract it and exploit it as required. Even if they fail to take the data outside the network’s walls, they can cause damage just by viewing it.
Results of Data Breaches
Data breaches can cause a lot of serious damage to both – the victim organization, and to individuals or firms associated with it, such as customers, employees, and partners. They can expose all types of personally identifiable information. The list includes, but is not limited to sensitive data such as names, phone numbers, birthdays, social security numbers, bank account details, debit and/ or credit card details, medical records, academic records, salary details, loan details.
(Source: After the Data Breach – What Happens to Your Data?)
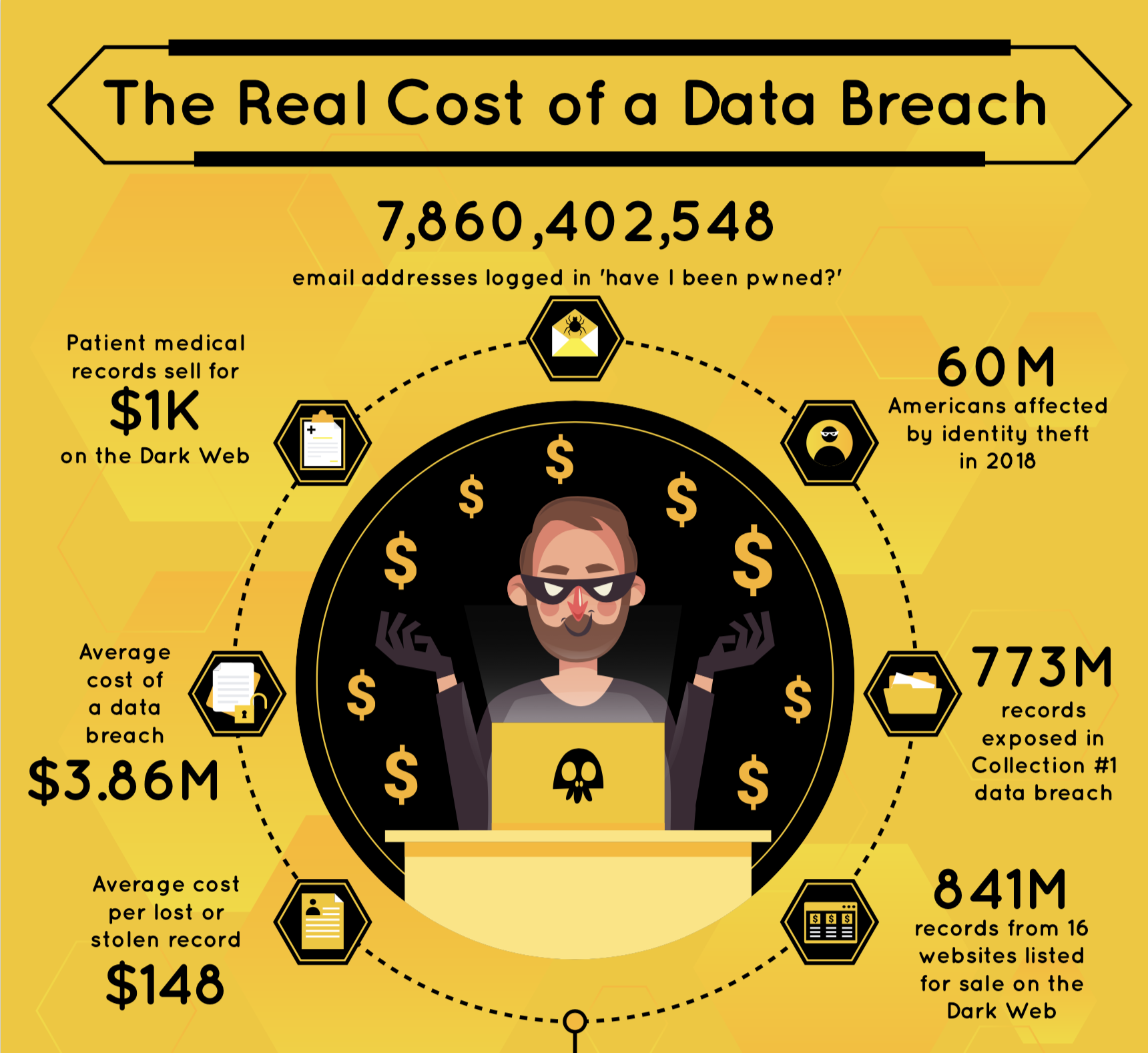
With stolen data being sold on the darknet for up to $2000, this is an extremely lucrative business for anyone who possesses the skill set to extract data. Due to the existence of a huge data market on the darknet, data breaches have become commonplace.
(Source: After the Data Breach – What Happens to Your Data?)
Data breaches don’t just mean stolen data, they also mean financial losses and damaged reputations. Studies show that on average, a data breach costs the victim organization $3.86M – affecting millions of individuals. A large number of victims directly translates into a loss of faith in the victim organization, severely affecting PR and marketing opportunities.
Best Practices To Prevent Data Breach
Now that you know just how dangerous data breaches can get, it is important to upgrade your organization’s security and minimize the risk of data breaches. Certain practices protect organizations against accidents and attacks that could lead to data breaches. We have provided a consolidated list of practices and policies you must enforce to stay as safe as possible:
Data Protection Regulations Compliance
In Europe, the General Data Protection Regulation (GDPR) was passed in 2018 to protect the privacy rights and personal data of individuals within the European Union.
Although the United States of America doesn’t have an equivalent all-encompassing security law, there are multiple federal and state-level laws that aim to protect the private data of citizens.
The federal laws are sector-specific, and state laws vary greatly but are effective for the time being. In 2018 itself, US senators proposed the Information Transparency & Personal Data Control Act, and the Data Care Act – both aimed towards creating a uniform set of regulations for data privacy across the country.
Depending on where your organization is located, you must go through the local data protection regulations and ensure everything is in order. In case there are no specific laws in your area, follow this list to cover all the basic principles of user privacy.
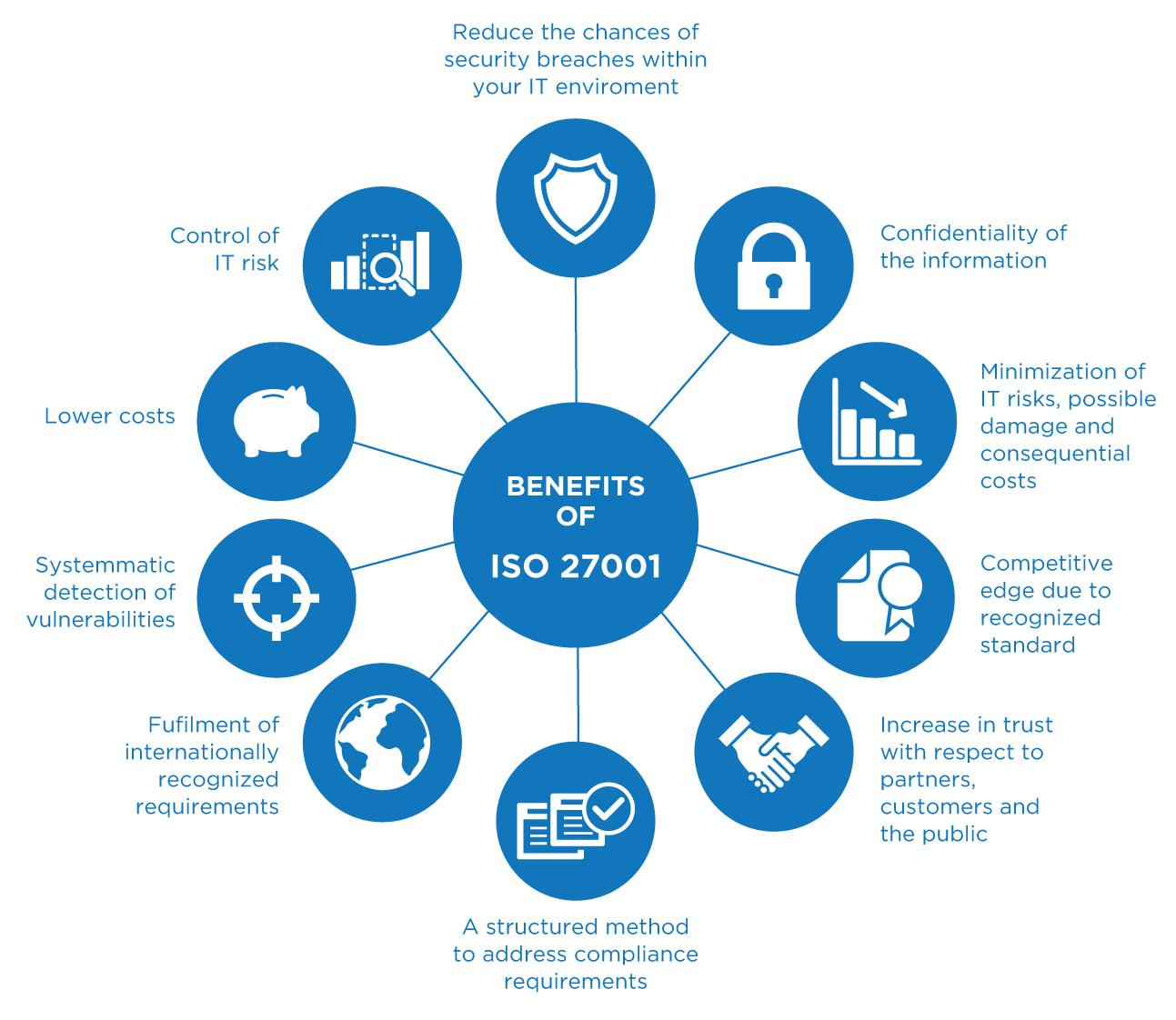
The International Organization for Standardization (ISO), in collaboration with the International Electrotechnical Commission (IEC), is responsible for the worldwide standardization of technical activities.
The ISO/IEC 27001:2013 “provide requirements for establishing, implementing, maintaining, and continually improving an information security management system” within organizations. Its adoption is extremely beneficial for any organization, due to the following reasons:
(Source: ISO 27001 Assessments and Implementation)
Maintenance of System Logs
System logging refers to the practice of recording system logs, for later review and analysis. Log monitoring and analysis aren’t just suggested practices, but necessary ones.
When carried out together, they allow us to capture system log files in real-time, view them, and analyze them. Doing so enables the detection and resolution of flaws in a system.
First, log files are automatically collected and responsible authorities are alerted about issues whenever one arises. Then, the actual analysis and repair take place.
Data Backups
Backing up data regularly is important as it minimizes data losses in the event of a destructive data breach. However, insufficiently protected data backups can be easily stolen, so these backups should preferably be cloud-based and regularly monitored.
Password Policy
Enforce a strong password policy on all employees, regardless of their user privilege. Make sure to keep the basics in mind:
15 character passwords including digits, uppercase letters, lowercase letters, and special characters are the strongest option, especially when they form an arbitrary phrase instead of predictable (set of) words.
Also, enable two-factor authentication across devices to make the protection stronger, and minimize endpoint risks.
Comprehensive Security Policy
Every organization should have a security policy that acts as a guideline for employees (including external vendors and partners). Since the needs, functions, and operations of every organization are different, the security policy has to be tailor-made. However, there are certain aspects which must not be overlooked, such as:
- User privilege: This security flaw is often overlooked by administrators, allowing users to engage with network modules that they have no relation to. To fix this issue, modules should give access to users based on their credentials and special authorization levels.
- Micro-segmenting: Micro-segmenting is the process of allowing users to access only those resources that they need. This is especially helpful for users dealing with the cloud, as it reduces network access and minimizes the risk of hackers finding entry points into the network.
- BYOD guidelines: In the 21st century, the Bring Your Own Device (BYOD) culture is prominent across the globe, especially in newer and younger organizations. Besides allowing employees to feel comfortable at work by maintaining an environment they’re familiar with, BYOD also improves productivity and saves time by allowing remote work. However, this means that every single remote (or unregistered) device is a new security risk. To tackle this issue, endpoint security measures should be strong and comprehensive.
- Exit strategy: When an employee leaves your organization, a certain purge must take place. Passwords, personally identifiable information, sensitive data, project matter – everything must be deleted from their desktop before it is handed over to a new employee. Not doing so exposes their data and allows attackers to exploit unsanitized systems.
Periodic Awareness and Auditing Exercises
It is unreasonable to expect every employee to have a strong knowledge of personal and organizational security. Although this is important, not everyone has had the opportunity to get an in-depth education surrounding it. As an organization, you could arrange for awareness campaigns for your employees. This would help them gain much-needed information regarding data security and minimize the risk of human error within your organization.
Additionally, it is a good idea to carry out regular auditing exercises to increase your knowledge about the potential flaws within your network. This helps with patch management and network strengthening.
Usage of Secure Technologies
A fatal step many organizations take is not doing a thorough background check of technologies they integrate into their products and network. Spending time and money on compatible and secure technologies not only reduces the risk of vulnerability exploitation but also saves money in the long term (if that’s a constraint for integrating a suitable option).
Another basic, but an important measure that must be taken is the encryption of all data. Whether your data is being sent out or stored somewhere, it should always be encrypted so that it can’t be used, if intercepted or stolen by attackers.
Effective Patch Management
It has been noted that even when organizations are informed about vulnerabilities present in their network, they choose to delay the patching process due to different reasons. While inadequate manpower, insufficient resources, and low finances are real problems, patch management should be fast and proper. Otherwise, attackers get an open window to cause maximum damage, which could lead to even higher financial struggles later on.
Timely Vulnerability Assessments
Patch management can take place after vulnerabilities have been detected, and vulnerabilities are hard to detect without dedicated efforts towards the same. For this reason, hiring security analysts for periodic vulnerability assessment exercises is a good security measure. This minimizes the risk of harmful security flaws slipping your notice.
Incident Response Plan
A functional Incident Response Plan (IRP) is of utmost importance in any organization. It makes damage control fast and effective in case a data breach takes place even after following every possible precautionary measure. To get an idea of how your organization should create its IRP, go through our thorough guide: