How to Investigate a Data Breach – Complete Guide

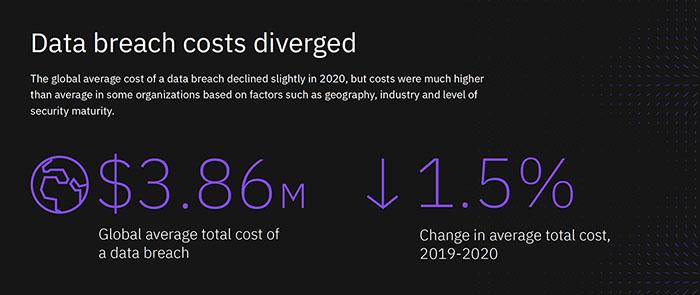
With over $100 million – $500 million being the projected cost of the CapitalOne hack in 2019, data breaches are no light issue. The Ponemon Institute’s Cost of a Data Breach Report published by IBM reveals that on an average, $3.86 million are spent by organizations facing a data breach.
Before answering how to investigate a data breach in detail, let’s have a look at some astonishing data by independent research labs.
(Source: Cost of a Data Breach Report)
These figures are based on the analysis of 524 data breaches across 17 industries – revealing that the healthcare industry loses $7.13 million on average, per data breach, with the United States of America being the most expensive country for organizations, at $8.64 million on average.
But where is all this money spent, and how does the process work? Now, costs such as fines, market losses, and image recovery always exist – but so does the actual investigation of the breach.
A data breach is essentially the intentional or accidental exposure of sensitive data to individuals or groups who aren’t authorized to access it. It’s dangerous because it violates every affected individual’s right to privacy and opens up the possibility of their personal data being sold and/ or misused otherwise.
Similar to other criminal investigations, a data breach investigation refers to the detail-oriented process of answering the “what, when, why, who, and how” of the incident.
Contents
- 0.1 How to Investigate a Data Breach
- 0.2 What did the breach affect?
- 0.3 When did it occur?
- 0.4 Why did the breach take place?
- 0.5 Who is responsible for the breach?
- 0.6 How did they succeed?
- 0.7 Pre – investigation:
- 0.8 Investigation:
- 0.9 Post – investigation:
- 1 Need for Data Breach Investigations
- 2 Tips for Successful Investigations
How to Investigate a Data Breach
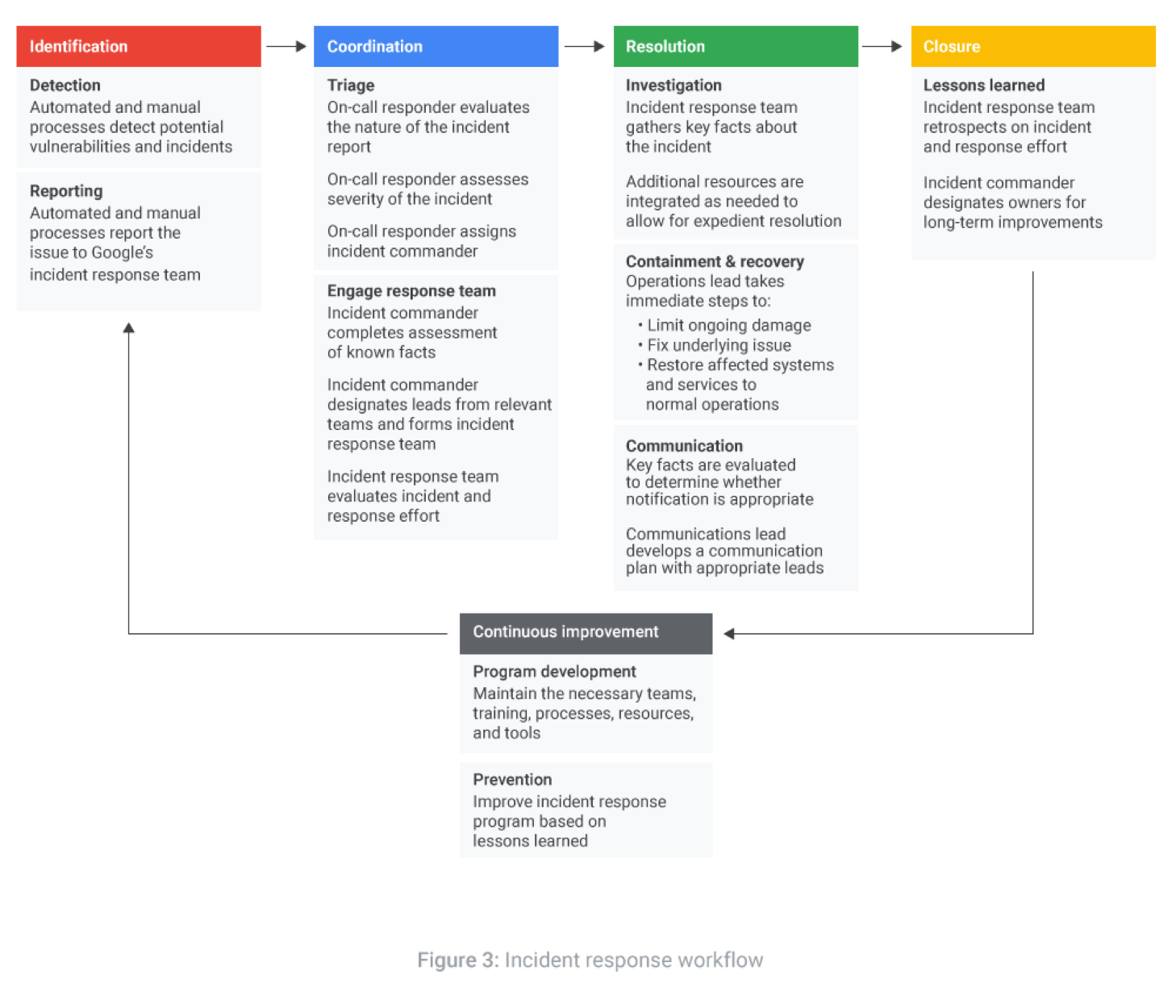
The investigation of a data breach involves finding out the origin of the breach, its extent, effects, and perpetrators. This is usually the first step of an Incident Response Plan, even though other tasks such as containing the breach and minimizing losses might seem more urgent.
The reason being, a data breach can be successfully isolated and contained only when its complete nature is known to the defense team – you can’t fix an issue unless you thoroughly familiarize yourself with its nature.
(Source: Google Cloud Data Incident Response Process)
Once the actual breach has been detected and initial intelligence has been gathered, the real investigation starts. This process broadly seeks to answer the following questions:
What did the breach affect?
Start by identifying the accounts, webpages, or systems that were definitely affected by the data breach. It’s a good idea to map out the entire attack. This allows you to see how the attack spread, if any patterns were followed and if the victims (accounts, webpages, or systems) have anything in common. This knowledge would make it easier to guess the attacker’s motives.
Endpoint Detection and Response (EDR) and Network Traffic Analysis (NTA) tools and services make this process fast, accurate, and efficient.
When did it occur?
Besides creating a map of the attack, a timeline should also be created. Not only would this provide more insight into the attack’s spread, but it would also allow you to analyze whether it could have been an inside job (depending on work timings).
Another reason why the timeline is important, is that some attacks can be carried out within very specific windows – such as during system maintenance, periods with extremely heavy network traffic, in – between security patches, etc. If the attack was launched during such a window, determining the attack vector becomes easier.
Why did the breach take place?
Understanding the motive behind the attack is extremely important. Once the motive is clear, it is possible to think from the attacker’s point of view. Doing so would enable you to predict their next step, in case the breach is ongoing. If you’re able to do this correctly, completely stopping the breach and possibly catching the perpetrator becomes easier.
Who is responsible for the breach?
Data breaches aren’t necessarily caused by malicious individuals. Sometimes, accidents and misuse by well-meaning employees can also result in data breaches.
(Source: Verizon 2020 Data Breach Investigations Report)
According to Verizon’s annual Data Breach Investigations Report, organized crime forms the highest percentage of threat actors – including funded or independent malicious individuals and organizations. However, innocent parties such as system administrators and end-users also form significant percentages of this demographic.
(Source: Verizon 2020 Data Breach Investigations Report)
Having basic knowledge about the attacker’s identity or affiliation helps the investigation process, as malicious actors would pose a higher risk, and have dangerous objectives which require quick and effective defense measures. On the other hand, accidental breaches can be dealt with at a slower, more relaxed pace, as the fear of misuse of data wouldn’t be present.
How did they succeed?
Manual investigation of system logs and/ or the utilization of digital forensics tools enable investigators to trace the attack’s progression and get a comparatively clear idea about the attacker’s identity – sometimes leading to complete detection.
By physically interviewing possible perpetrators, going through system log files, analyzing the activity of employees and other IP or MAC addresses, etc, it is possible to understand who was active during which stage of the attack.
Identifying each (exploited) vulnerability in the organization’s network, and determining which tools and types of attacks made the breach possible enables you to understand the entire life-cycle of the data breach, making the patching process faster.
The answers to these questions allow breach investigators to experience the data breach as if in real-time, by following a certain procedure:
Pre – investigation:
Data security requires foresight. Data breach investigations can’t be carried out effectively if nothing is monitoring the organization’s network and detecting abnormalities.
For this reason, a monitoring solution consisting of an Intrusion Prevention System, Intrusion Detection System, or Endpoint Security solution must be configured beforehand. These solutions monitor the network 24×7 to detect malicious activity, trace workflows tainted with suspicious behavior, and provide logs that can be manually analyzed if need be.
Investigation:
This step utilizes all the data and network security tools or services being used by the organization. It can be manual, automated, or hybrid (advisable). The actual investigation process involves the collection of breach-related data, its analysis, theorizing, interviewing relevant employees and/ or partners, documenting each discovery, and keeping affected parties up-to-date with the progress.
The investigation process requires coordination and communication amongst the organization’s Incident Response Team, temporary or permanent security analysts, law enforcement bodies, digital forensics experts, and any other relevant entity. By working together, they can speed up the process and ensure no stone stays unturned.
Post – investigation:
Once all the facts and details of the data breach are known to you, they should be collated and published publicly. This is an important step, as outsiders should receive honest information from the organization itself, not third-party sources. Once a statement has been released, other victims of the data breach should be privately contacted and informed about it.
Information such as when the breach took place, how much data was exposed, how much of their data was exposed, and the current status of the recovery process should be communicated to them. The victims should also be offered help in the form of resources to protect their security, and monetary or favor – based apology tokens.
Once this entire process has been completed, it is important to review every security misconfiguration and patch all vulnerabilities. Proactive security management is the only valid form of security management.
Need for Data Breach Investigations
Data breach investigations aren’t optional. Efficient, fast, and accurate investigations are an absolute necessity for any organization suffering from the aftermath of a potential data breach, as it guarantees the following:
Nature of the breach
Unless a proper investigation takes place, you can’t be sure when it occurred, how it occurred, who was behind it, and what their motive was.
Knowledge about the extent of the breach
Investigations don’t just confirm data breaches, they tell you how much damage has been done. It is important to know exactly how much (and which type of) data got affected. This helps you understand the attacker’s motive and specific target (s) while giving a clear idea of how the recovery process should proceed – based on the type and amount of the affected data.
Enables mitigation and remediation
Mitigation and remediation in the wake of data breaches refer to the isolation of network elements, PR damage control, patching of vulnerabilities, and improving overall security. These steps can’t be done without having complete knowledge of the breach – hence, the investigation’s necessity.
Minimizes current and future losses
Timely investigations translate into timely remediation, reducing market losses and customer dissatisfaction – saving money. During the investigation, compliance with data security regulations is also checked, thus minimizing the risk of avoidable errors. Also, the investigation documentation can be used as a reference during future security incidents – saving time, money, effort when that happens.
Tips for Successful Investigations
Nobody is immune to a data breach, but some are more adept and prepared at dealing with them. To ensure you’re a part of this group of people, always keep the following in mind:
- Even before the actual breach takes place, certain measures should already be placed. Breaches can’t be avoided, but they can be handled quickly and efficiently by using tools and services built for this. Always secure your organization’s network and physical space with effective firewalls, antiviruses, a tight security policy, and Intrusion Prevention Systems.
- Create a dedicated investigation team for data breaches, which may be a part of your organization’s internal or hired Incident Response Team. Make sure it’s multidisciplinary – including security analysts, network and system administrators, PR handlers, legal representatives, and customer service members.
- Be thorough with the investigation – do not leave any vulnerability untouched or unexplored. Trace all the affected data back to its source and examine it properly. Employ digital forensic experts and manual investigators for this process.
- Keep the legal fee in mind – lawsuits and regulatory fines come complimentary with data breaches. Allocate enough funds for the same beforehand, to minimize the struggle.
- Be proactive. Data breaches are a result of exploited vulnerabilities, so make sure you don’t have any in the future. Every network, system, and web application is at the mercy of its developers and maintainers. Human error is a constant risk, but it can be minimized with regular reviews and thorough security checks.